Offensive Security Tools
tl;dr: yes, defenders need them too
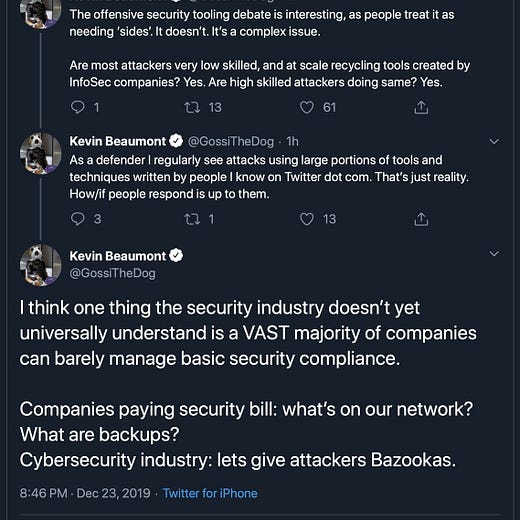
#InfoSec Twitter has blown up over the past few days in a renewed debate over offensive security tools.
I don’t think I have much expertise to add to the debate, except to say that as someone who plays InfoSec defense for a living, I gleaned most of my current knowledge by playing around with red team tools.
Would I publish one? Probably not, if I’m being honest. Would I feel differently about this topic if I was tasked with defending a Windows 2012 environment, that wasn’t scheduled to be patched or upgraded for months? Probably.
Playing tennis against a wall doesn’t increase your skill as fast as playing against an adversary. Personally I’m grateful for the democratization of offensive security tools as a free crash course in becoming better at my job.